Cryptocurrency gives users full control over their assets, but it also means security becomes a personal responsibility. A large part of protecting your crypto accounts comes down to understanding the basics: strong passwords and proper two-factor authentication.
Many attacks against crypto users don’t involve advanced hacking techniques. Instead, attackers rely on stolen passwords, phishing websites, or compromised devices. A solid security setup makes these attacks significantly harder.
The Password Is Still the First Line of Defense
Every serious security setup starts with the basics: a strong password.
Not a recycled one. Not a variation of an old one. A proper, long, unique password — ideally 16 to 20 characters — mixing uppercase letters, lowercase letters, numbers, and symbols. The difference between an average password and a strong one isn’t theoretical.
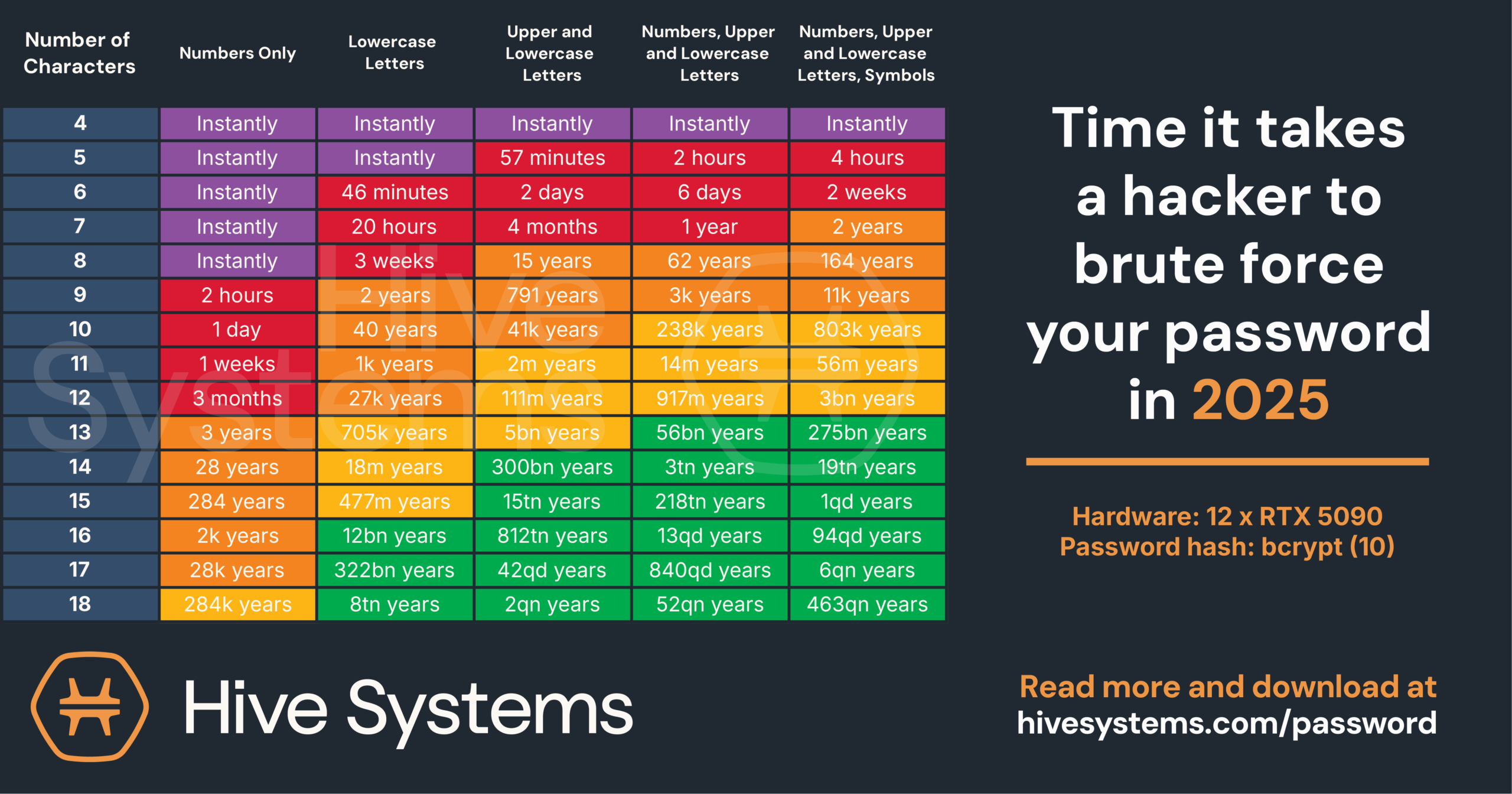
Research from Hive Systems shows that the time required to crack a password increases exponentially with its length and complexity. What takes seconds in one scenario can become computationally unrealistic in another. According to the password-cracking table published by Hive Systems, even a six-character password combining letters, numbers, and symbols could still be cracked in roughly two weeks using modern hardware.
We used to be told to change passwords frequently. That recommendation has evolved. Frequent password changes often lead to weaker patterns or predictable variations.
Today, the priority is using a unique and strong password for every service, especially for platforms that manage financial assets like cryptocurrency exchanges or wallets.
For cryptocurrency owners, a strong password is essentially the front door lock protecting their crypto accounts. But the real question is: what happens if someone gets hold of that password?
Unfortunately, phishing websites, data leaks, malware, and social engineering attacks are common. Once login credentials are exposed, the security of your account depends entirely on what sits behind that password. That is where two-factor authentication (2FA) becomes essential.
Why Two-Factor Authentication Matters for Crypto Security
Two-factor authentication simply means proving your identity in two different ways.
It usually combines:
- something you know (your password)
- something you have (a device or security key)
- or something you are (biometrics)
This additional verification layer significantly improves crypto security. Even if someone obtains your password, they still need access to the second factor.
However, not all 2FA methods offer the same level of protection.
Where the Differences Between 2FA Methods Matter
SMS Verification
SMS verification is still widely used because it’s familiar. You log in, receive a code, and enter it. The problem is that phone numbers were never designed to serve as a secure layer for protecting financial systems. During a SIM swap attack, attackers can take control of a phone number and intercept verification messages, including login codes.
For high-value accounts such as cryptocurrency exchanges, SMS should generally be considered a weak form of two-factor authentication.
Email Verification
Email-based codes are only as secure as your email account. Many crypto platforms use email for password resets, transaction confirmations and withdrawals. If someone gains access to your email account, they may potentially take control of several services connected to it. This is why securing your email account is just as important as securing your crypto accounts.
Authenticator Apps
Authenticator apps, such as Google Authenticator, generate time-based codes for crypto account security directly on your device. After installation, you scan a QR code provided by the service to link your account to the app, after which time-based one-time passwords (TOTP) are generated. As these codes are created locally on your device and do not rely on phone networks, the risk of certain types of attack is significantly reduced.

Don’t forget to back up your 2FA and store it somewhere secure—on paper or in a password manager. The goal is to keep attackers out without accidentally locking yourself out. We talked about this issue in this previous article.
Since nothing travels through phone networks, the risk of attack using time-based codes is reduced. For a lot of users, this hits the sweet spot between usability and security.
Some authenticator apps also include additional protections. For example, enabling the Privacy Screen in Google Authenticator restricts access using Face ID or biometric authentication.
This feature can make a real difference. In one case we assisted with, a crypto user had his phone stolen near a crypto event while using Google Maps to navigate. Because the device was unlocked at the moment of the theft, the attacker gained immediate access to both the crypto account and the authenticator app, allowing funds to be stolen.
Push-Based Authentication
Another form of 2FA is push-based approval. Rather than entering a code, you receive a notification on a trusted device and can approve the login request with a single tap. This method is efficient, as long as the user verifies the approval request is legitimate before confirming.
Hardware Security Keys
Hardware security keys provide one of the strongest forms of two-factor authentication. Devices developed by companies such as Yubico rely on public-key cryptography and physical possession of the key. There are no transferable codes, SMS messages, or approval notifications. Authentication is bound directly to the hardware device, which makes phishing attacks significantly more difficult.
Passkeys
Passkeys are a newer way to log in without remembering a password. Instead, your device — like your phone or laptop — securely handles the authentication. When logging in, you often use biometrics such as Face ID or a fingerprint.
The benefit? Logging in becomes faster and easier, and it’s much harder for attackers to compromise your account, since there’s no password they can steal or phish. As more platforms adopt passkeys, they could eventually replace traditional passwords, making your crypto accounts even more secure.
If a service offers two-factor authentication, it should always be enabled. Whenever possible, choose time-based authenticator apps or hardware security keys as your preferred 2FA method. These options offer stronger protection than SMS or email verification.
For anyone managing cryptocurrency, these basic security steps can make the difference between a secure account and a potential loss of funds.
FAQ
How do most crypto accounts get hacked?
Most crypto accounts are compromised through phishing attacks, stolen passwords, or weak two-factor authentication. Attackers often trick users into entering login credentials on fake websites or gain access through data leaks. At Tracelon we frequently see cases where accounts were protected only by a password, making them easier for attackers to take over.
What is the safest way to secure a crypto account?
The safest approach is using a long, unique password combined with strong two-factor authentication. Security professionals recommend authenticator apps or hardware security keys instead of SMS codes. This creates an additional layer of protection, meaning attackers cannot access an account even if they obtain the password.
Can hackers bypass two-factor authentication?
Two-factor authentication significantly improves security, but phishing and social engineering attacks can still pose a risk. Using stronger methods, such as authenticator apps or hardware security keys from companies like Yubico, enhances crypto account security because authentication is tied directly to a device.