Crypto security tips are essential to avoid losing your digital assets. In this guide, we explain how to protect your wallet, avoid phishing risks, and follow best practices to stay safe.
Crypto Security Tips: Protect Your Wallet
One of the most important rules is simple: never let others know you own crypto.
It sounds obvious, but it is often ignored. If you post on X or other social media that you own crypto, especially if it is a significant amount, you can easily turn yourself into a target.
Privacy is your first layer of crypto security
In crypto, visibility is risk. You do not need to show your wealth. It only increases your risk. So do not publicly share wallet addresses that are connected to significant funds, or post screenshots of your balances or gains.
Use your knowledge to contribute to the space, but do not expose yourself in ways that make you easier to target. Unfortunately, there are real cases of people being approached, followed, or singled out after speaking too openly about crypto online.
ENS and on-chain identity exposure
A good rule of thumb is to keep your exposure minimal, including how you use ENS names.
ENS in particular makes things interesting. It is a powerful tool for usability and identity on-chain, but it also creates a visible link between your activity and your identity. If not used carefully, it can make it easier to connect wallets, track behavior, and build a picture of your holdings.
For that reason, it is often better to keep ENS names away from your primary storage wallets and use them more for interaction than for holding value.

How to react after phishing or crypto fraud
If you ever become the victim of phishing or fraud, the way you react is just as important as the initial incident. Do not make it public.
Unfortunately, many people get targeted a second time after being compromised. Scammers often pretend to be recovery experts, claiming they can retrieve lost funds in exchange for an upfront payment.
If someone promises to return your crypto, it is fake. In almost all cases, this is simply another attempt to steal from you.
Securing your devices and exchange accounts
Security also extends to the devices you use every day. If you have exchange apps installed on your phone, you should treat that device as something that holds real value. In traditional terms, it is no different from carrying access to your bank account in your pocket.
That means strong passwords, proper two-factor authentication, and preferably not relying on SMS-based verification. Biometric authentication and multiple confirmations for withdrawals can add another layer of protection. You can find out more about this topic in a previous article.
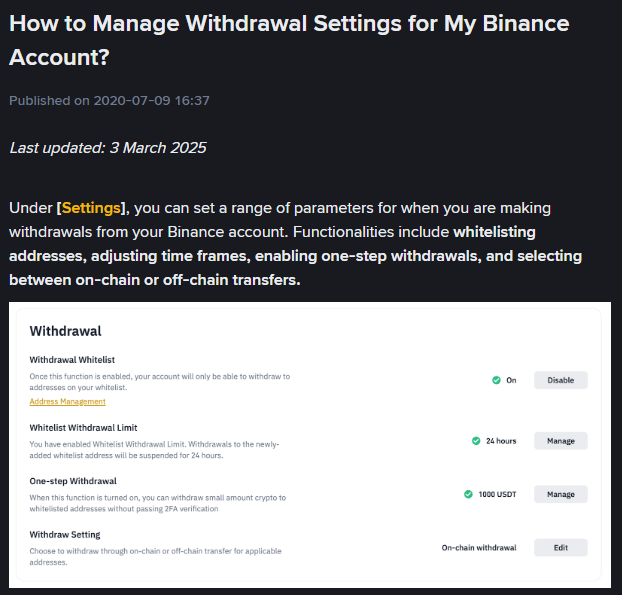
If you do keep assets on exchanges, it is worth exploring the security settings they provide. Features like withdrawal whitelisting or delays for new addresses can make a real difference if your account is ever compromised. Exchanges such as Binance provide detailed explanations on how to set this up properly.
Hardware wallets and long-term crypto storage
For longer-term holdings, a hardware wallet is still one of the most reliable options. It may feel a bit technical at first, but once set up, it significantly reduces your exposure to online attacks such as phishing or compromised exchanges or services.
Seed phrase security is critical
And then there is the seed phrase, which remains the most critical element of all. Never store it online — not in email, not in cloud storage, not on your phone, and not on your computer.
Most attacks still happen digitally, not physically, and once a seed phrase is exposed, there is no recovery path.
It should be stored offline, in a way that is durable and resistant to damage, and ideally in more than one secure location. The goal is not just to protect it from theft, but also from loss due to accidents or hardware failure.
Crypto security is about habits, not one decision
In crypto, security is rarely about one big decision. It is the accumulation of small habits that reduce your exposure over time. These crypto security tips focus on consistency rather than single actions.
The less you reveal, the fewer connections you create between identity and funds, and the more deliberate you are with storage, the safer you become.
Tracelon support for crypto fraud and phishing cases
At Tracelon, we provide a free initial assessment for cases involving crypto fraud or phishing. The goal is to carefully review what happened, understand how the incident likely occurred, and determine whether any realistic next steps are available based on the situation.
This is not about making promises, but about bringing clarity in a space where uncertainty and misinformation are common.
FAQ
Is it safe to share my crypto wallet address publicly?
A wallet address on its own is not always dangerous, but when it becomes linked to your identity or known holdings, it can increase your exposure. Attackers often combine small public details to identify potential targets.
Why do scammers target crypto users?
Because crypto transactions are irreversible and often harder to trace in real time. Combined with public exposure on social media, it creates an environment where targeted attacks can be highly profitable for scammers.
What should I do if I get scammed or phished?
First, secure all remaining accounts and devices immediately. After that, be extremely careful with anyone claiming they can recover your funds, especially if they ask for upfront payment. Recovery scams are very common in the crypto space.
While these crypto security tips can significantly reduce the risk of fraud and phishing, they cannot eliminate it completely. Incidents can still happen. In such cases, Tracelon can provide a free initial assessment to understand what happened and explore possible next steps.